

AI tools have made it trivially easy to spin up convincing phishing sites, impersonation domains, and brand spoofs at scale. The volume of these attacks is growing faster than most teams can manually triage. This project explores how to automate the detection-to-enforcement pipeline while keeping accuracy high - scanning for suspicious domains, enriching them with real threat intelligence, scoring risk with compound signals, and routing only credible threats into the case workflow.
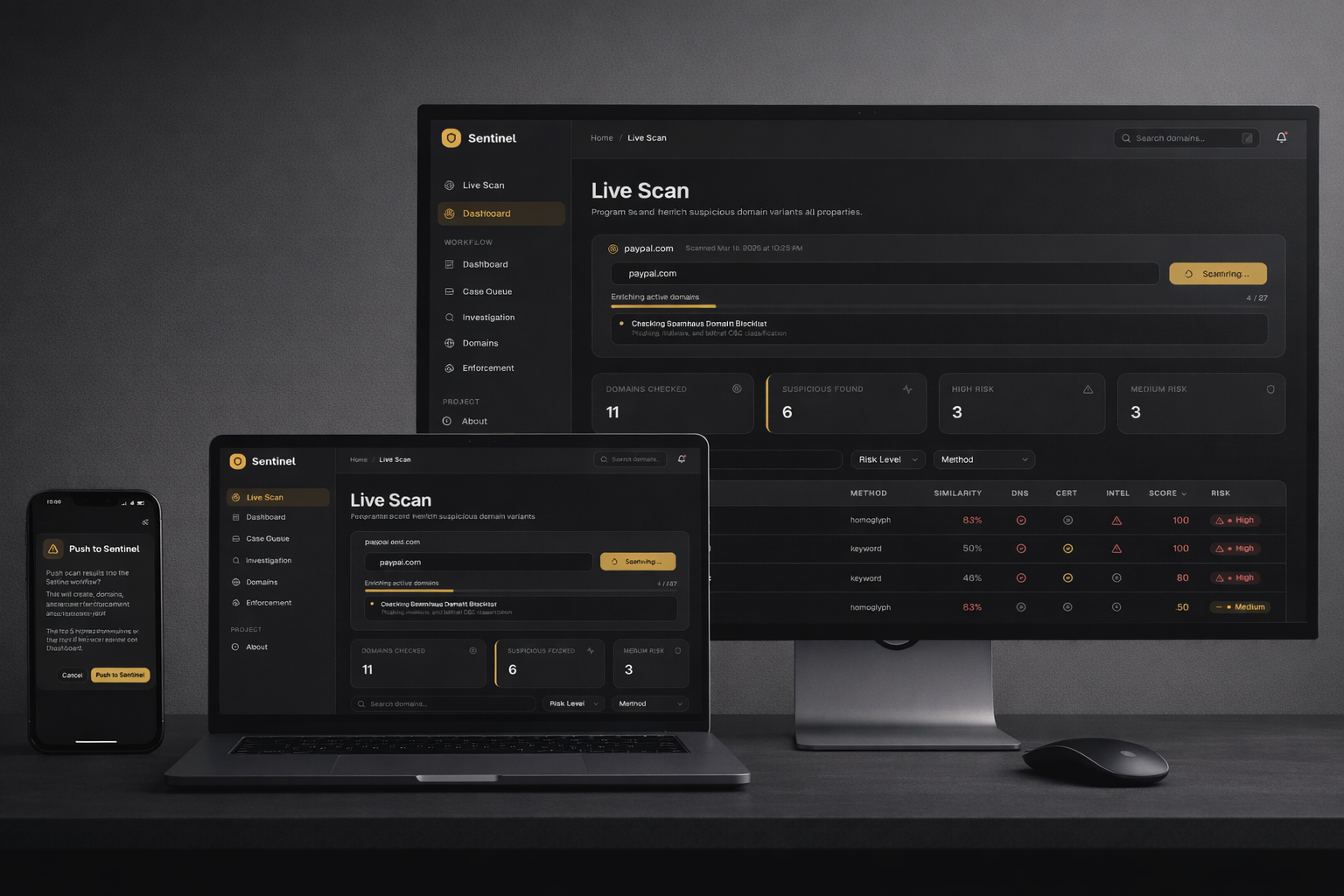
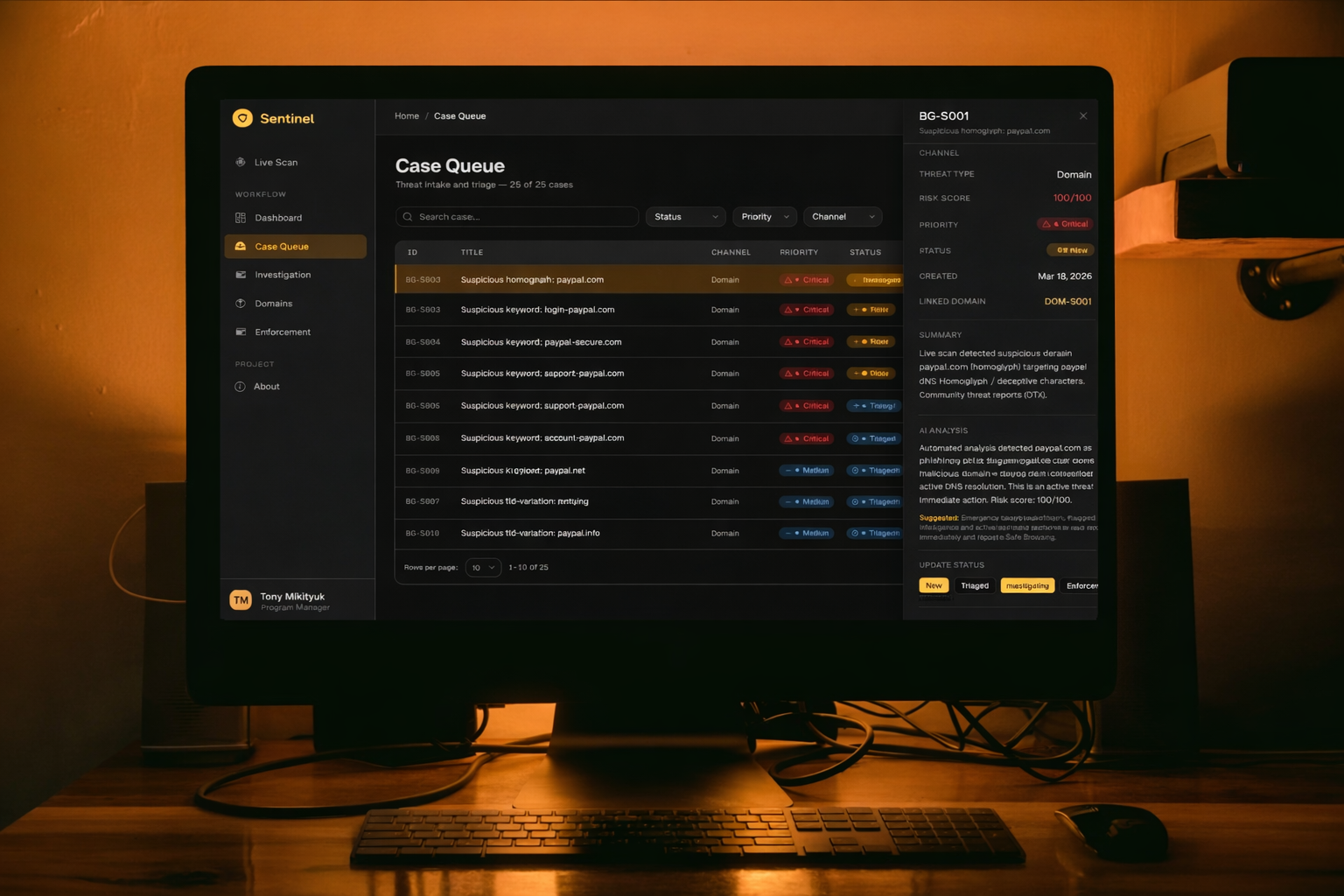
Enter any brand domain and the engine generates 20+ suspicious variants using 8 techniques (homoglyphs, typosquatting, TLD swaps, keyword injection, character deletion, transposition). Each variant is probed against Google DNS-over-HTTPS, then enriched with RDAP registrant data, Certificate Transparency logs via crt.sh, Spamhaus blocklist status, URLhaus malware checks, and AlienVault OTX threat intelligence. All real APIs, no mocked data.
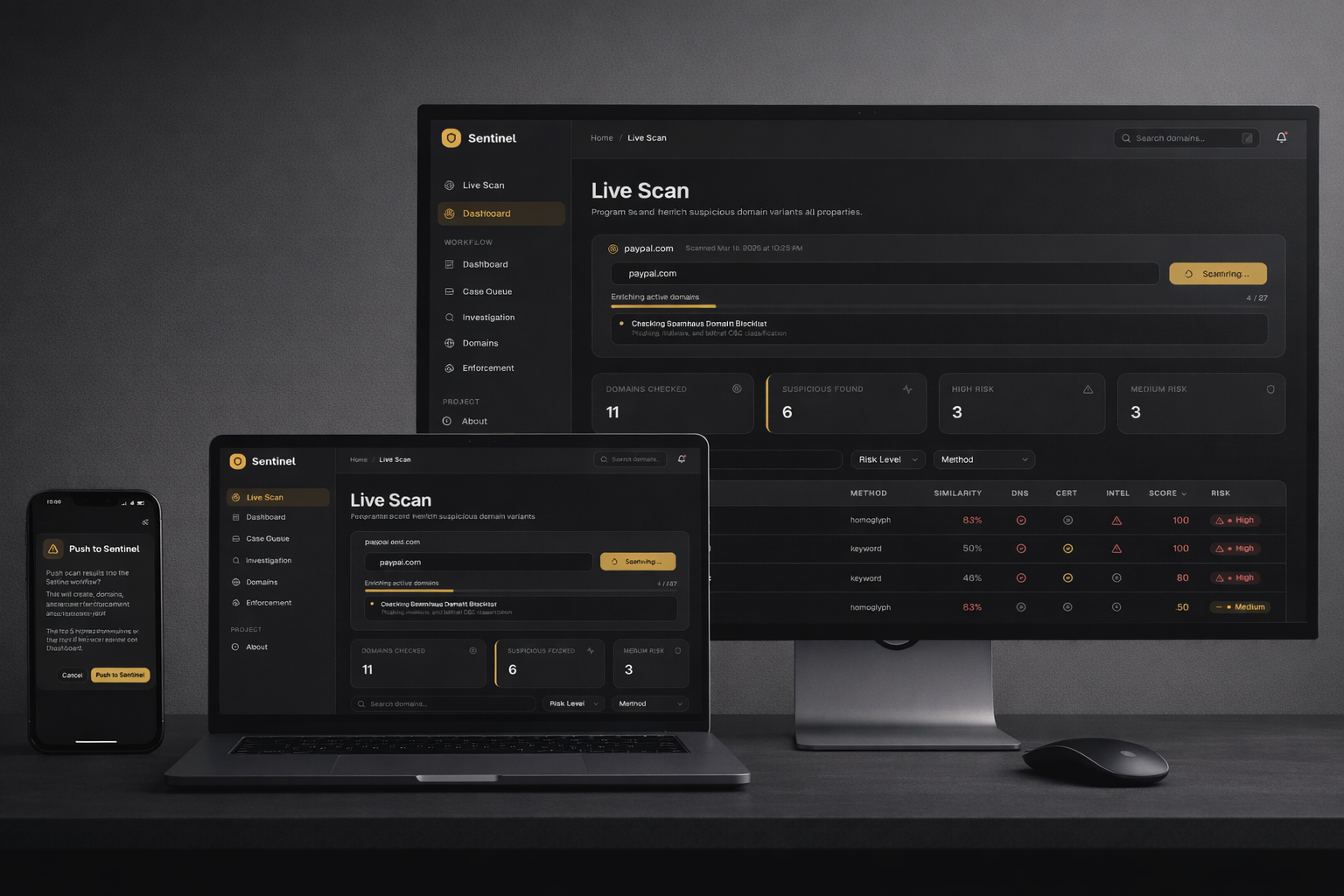
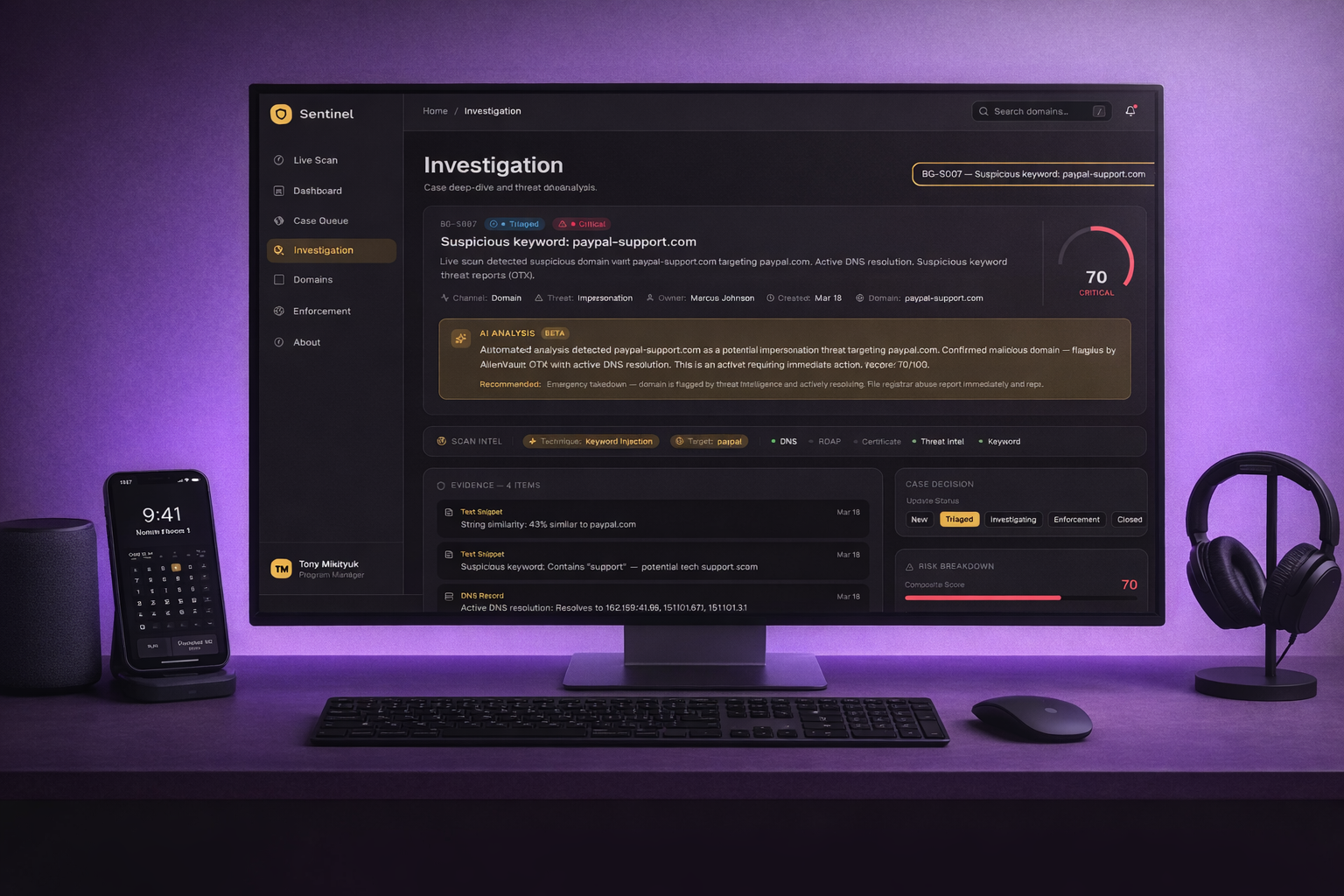
A compound scoring model weighs DNS resolution (40), certificate recency (20), registration age (20), keyword match (25), homoglyph similarity (15), and registrant trust signals (10) to classify each domain as Low, Medium, or High risk. The top 5 threats surface in an interactive AI Triage card with signal-aware analyst summaries and recommended enforcement actions - agree to auto-escalate, or flag for manual investigation.
One scan populates the entire application: cases are created in the queue, domains are registered in the portfolio, evidence is attached (DNS records, WHOIS snapshots, certificate logs), and enforcement actions are routed to 4 vendor partners with SLA tracking. The workflow mirrors how enterprise brand protection programs actually operate - detection, triage, investigation, enforcement, resolution - with every entity cross-linked and navigable.
End-to-end product thinking applied to a security operations domain: scoping a 7-page React application with real API integrations, designing a compound data model with cross-entity relationships, building a custom design system (Torch Dark Gold), and shipping a production deployment to GitHub Pages - all through AI-assisted development with Claude Code. The project shows how someone with program management instincts approaches technical builds: workflow-first, data-driven, and systematically organized.
"The best security tools don't just find threats - they turn detection into action. This dashboard bridges the gap from scan result to takedown request."